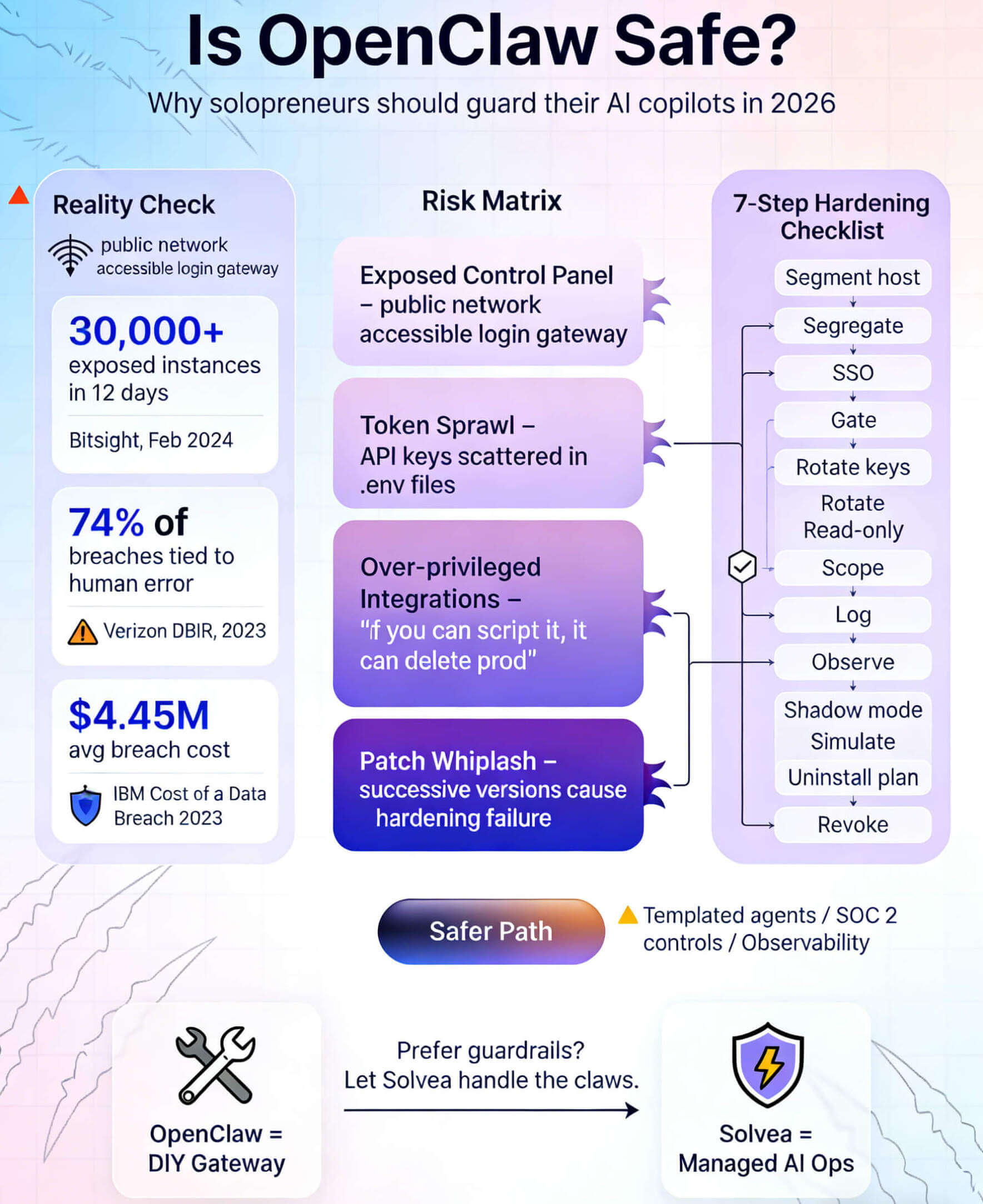
Quick Answer: OpenClaw is powerful but not inherently safe. Bitsight researchers observed 30,000+ exposed OpenClaw instances between January 27 and February 8, 2024, meaning thousands of unsecured agents were reachable from the open internet. Unless you can harden Linux servers, manage API keys, and monitor every integration, you risk handing unfettered access to your calendars, inboxes, and SaaS tools to an unmatured agent.
Why the Question Matters Now
Solopreneurs are embracing AI copilots faster than enterprises. Stripe Atlas reports that a typical one-person SaaS stack now includes 12+ connected apps ranging from CRMs to invoicing tools. When you bolt OpenClaw onto that stack, you grant an agent root access to everything from Slack to bank notifications. According to IBM’s 2023 Cost of a Data Breach report, the global average breach costs $4.45 million, a figure that startups obviously cannot absorb. Even if you “only” leak 1,000 customer emails, the reputational hit can cripple a young brand overnight.
Is OpenClaw Legit or a Liability?
OpenClaw is open-source and actively maintained, so in that sense it is “legit”—you can audit the code, self-host it, and extend it freely. However, legitimacy does not equal safety. The project creator explicitly warns, “Most non-techies should not install this.” That warning exists because OpenClaw:
1. Runs as a privileged control plane that can execute shell commands, send emails, and edit files.
2. Relies on user-supplied API keys for messaging, cloud, and LLM providers.
3. Exposes a web control panel that, if left unsecured, offers attackers direct command of your agent.
In other words, OpenClaw is only as safe as the person configuring OAuth credentials, reverse proxies, and firewall rules. Verizon’s 2023 Data Breach Investigations Report attributes 74% of breaches to the “human element”—misconfigurations, stolen credentials, or social engineering. OpenClaw magnifies this risk because a single typo in .env or an improperly secured tunnel can expose the entire assistant.
Documented OpenClaw Security Issues
Risk | What Happens | Why It Matters |
Internet-Exposed Instances | Bitsight found 30,000+ gateways reachable from the public web in a 12-day window. | Attackers can sign into the panel, view logs, and trigger automations remotely. |
Token Sprawl | API keys for WhatsApp, Slack, GitHub, and cloud services sit in plaintext config files. | A compromised host yields full API access across every connected platform. |
LLM Supply Chain | Users often connect undisclosed third-party LLM endpoints to save money. | A malicious LLM proxy can log prompts and steal downstream credentials. |
Integration Overreach | OpenClaw encourages “if you can script it, the agent can do it.” | Without least-privilege controls, the agent can wipe databases or send fraudulent invoices. |
Patch Discipline | Releases move fast; February saw five breaking changes in eight days. | Solo founders rarely have time to reapply hardening steps after every update. |
OpenClaw’s documentation does provide setup guidance, but it lacks an enterprise-grade hardening guide. If you want those guardrails, you’ll have to write your own Ansible playbooks or look for platforms with prebuilt templates such as Solvea’s OpenClaw alternatives guide.
Security Checklist for the Brave DIYer
If you still plan to experiment with OpenClaw, treat it like any other production workload. Use this abbreviated checklist before letting it touch customer data:
1. Segment the host. Deploy on a zero-trust segment or cloud VM with inbound traffic locked to your IPs.
2. Enforce SSO on the control panel. Hide the UI behind OAuth or mutual TLS; never expose it directly.
3. Rotate credentials weekly. Store API keys in a secrets manager rather than .env files.
4. Use read-only scopes first. Give the agent view access to calendars and CRMs before enabling write actions.
5. Log every action. Ship gateway logs to a SIEM so you can roll back unexpected commands.
6. Shadow mode. Run automations in “dry run” for seven days, then gradually enable destructive actions.
7. Plan the uninstall. Keep a runbook for nuking the VM, revoking tokens, and notifying partners if exposure occurs.
This seven-step process may take 8–10 engineering hours to implement the first time. If that sounds daunting, it is a strong signal that OpenClaw might not match your current risk appetite.
A Safer Alternative: Solvea
Solvea is a managed AI operations platform that lets you build autonomous copilots without babysitting your own gateway. Instead of hand-wiring every integration, you describe the workflow and Solvea delivers governed execution across channels.
If you're trying to ship an assistant quickly, the Build Agent with Template wizard walks you through scoping permissions, mapping tools, and launching on WhatsApp, Slack, or email in minutes. If data hygiene is the worry, the Sync from Platforms playbook ingests CRM, ecommerce, and support records through audited connectors so you never paste raw API keys into .env files again.
Solvea capability | What it does | Why it matters vs. OpenClaw |
Templated agent builder | Launches multi-channel agents from vetted blueprints with scoped permissions. | No need to expose a DIY control panel or manage OAuth scopes manually. |
Audited data syncs | Pipes CRM, ecommerce, and ticket data through governed connectors. | Eliminates plaintext API keys and reduces data leakage risk. |
Governance controls | SOC 2-aligned logging, rate limits, and approval flows. | You inherit security reviews and 5 trust service criteria instead of writing policies yourself.[^aicpa] |
Observability & recovery | Built-in action logs, rollbacks, and alerting. | Gives solopreneurs the safety net of an ops team when automations misfire. |
Because Solvea ships as a service, you also get patch management, credential vaulting, and enforced least privilege. That keeps the focus on customer work while the platform keeps the "claws" where they belong—inside a secured boundary.
FAQ
Is OpenClaw legit?
Yes—it’s an open-source project with an active community. However, “legit” does not mean production-ready. Without enterprise-grade controls, OpenClaw remains a hobbyist tool that can jeopardize business data.
What are the biggest OpenClaw security risks?
The top risks are exposed control panels, plaintext API tokens, over-privileged integrations, and rapid release cycles that erase manual hardening. Any one of these gaps can let adversaries operate your agent remotely.
Can I harden OpenClaw enough for client work?
If you have DevSecOps experience, you can sandbox OpenClaw inside a locked-down VPC and wrap it with SSO, logging, and automated patching. That said, most solo founders find it faster to adopt a managed alternative like Solvea that was built with governance in mind.
Conclusion
OpenClaw is a fascinating glimpse into the future of persistent AI agents, but “Is OpenClaw safe?” remains a valid concern—especially for solopreneurs without security teams. When dozens of thousands of control planes are exposed online in less than two weeks, the burden of proof falls on the deployer, not the tool. Use the checklist above if you must self-host, but consider channeling your automation ideas into Solvea instead. You’ll still get cross-channel AI copilots, yet you’ll do so inside an environment engineered to protect customer trust.












![The 10 Best AI Email Assistants in 2026 [Tested & Reviewed]](https://cdn.shulex-voc.com/shulex/upload/2026-03-03/d8f69c8e-5b60-4ee3-879b-2197c44d88cf.png)